TL;DR
A CMDB creates value when it connects services to the components that affect them. A CMDB fails when it becomes an unowned inventory that nobody trusts.
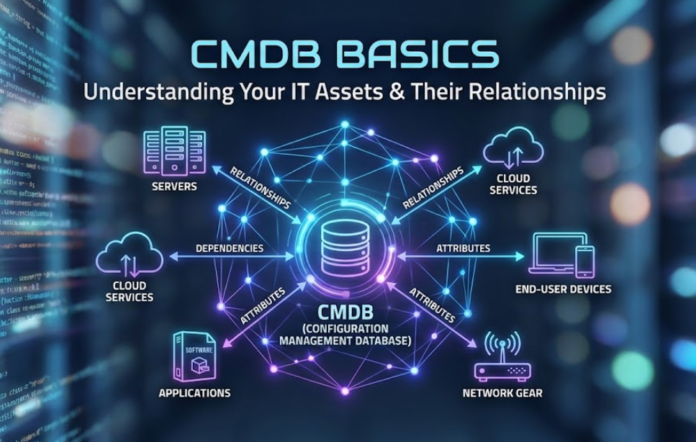
What a CMDB is, in plain terms
A Configuration Management Database stores configuration items and their relationships. The purpose is operational: understanding impact, improving incident resolution, and making changes safer.
A question that prevents wasted effort is: Do we need relationship visibility, or do we only need asset tracking?
If you only need asset tracking, start there and add CMDB depth later.
What to model first
The best approach is to start small:
- A list of key business services
- Critical applications that support those services
- Key infrastructure components that can bring services down
- Owners and lifecycle states for each critical item
Relationships that deliver the highest value
You do not need deep modeling to get results. Start with:
- Service to application
- Application to key infrastructure
- Incident to service
- Change to service
Teams often ask, Should we model every endpoint as a CI?
Only if endpoints materially affect your incident volume and you have a reliable way to keep data current. Otherwise, treat endpoints as assets and link them where it matters.
How to keep the CMDB from degrading
CMDB quality is a governance problem more than a tooling problem. Focus on:
- Ownership for critical items
- Review cadence for high-impact services
- Required fields that prevent “unknown” records
- Simple audits for duplicates and stale items
- Automation for discovery where possible
Signs your CMDB is not trusted
- Many records have no owner
- Many items are in an unknown state
- Incidents and changes are not linked to services
- Engineers avoid using CMDB data in impact discussions
If people avoid the CMDB, ask this: Are we capturing data that helps daily decisions, or are we capturing data because it seems “complete”?
Daily usefulness beats completeness.
A practical 60-day plan
- Days 1–15: define services, owners, and a minimal CI model
- Days 16–30: link incidents and changes to services for high impact cases
- Days 31–45: add key relationships and basic quality checks
- Days 46–60: review reporting and expand only where it improves outcomes
Closing thought
A working CMDB is smaller than most people think. It is owned, used daily, and focused on services and impact.